Application Process
To use the API, you first need to apply for the corresponding service on the hCaptcha Protocol Recognition API page. After entering the page, click the “Acquire” button, as shown in the image below: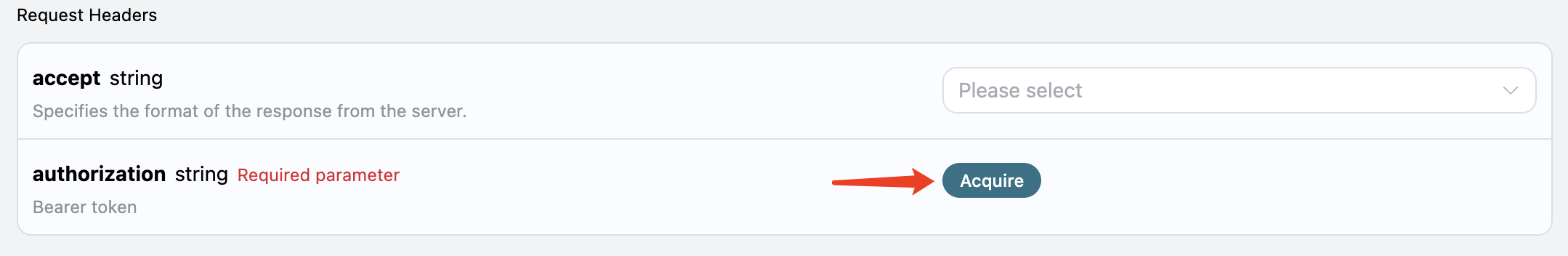 If you are not logged in or registered, you will be automatically redirected to the login page inviting you to register and log in. After logging in or registering, you will be automatically returned to the current page.
There is a free quota available for first-time applicants, allowing you to use the API for free.
If you are not logged in or registered, you will be automatically redirected to the login page inviting you to register and log in. After logging in or registering, you will be automatically returned to the current page.
There is a free quota available for first-time applicants, allowing you to use the API for free.
Basic Usage
First, understand the basic usage method, which is to input the URL of the website that needs to process the hCaptcha verification code to obtain the processed result. You need to simply pass awebsite_url field. Our example website is: https://accounts.hcaptcha.com/demo. We need to obtain the website_key from the website_url page. First, open this webpage, press F12 to enter the console, and then perform a global search for hcaptcha-demo in the Elements page. We can get the following result:
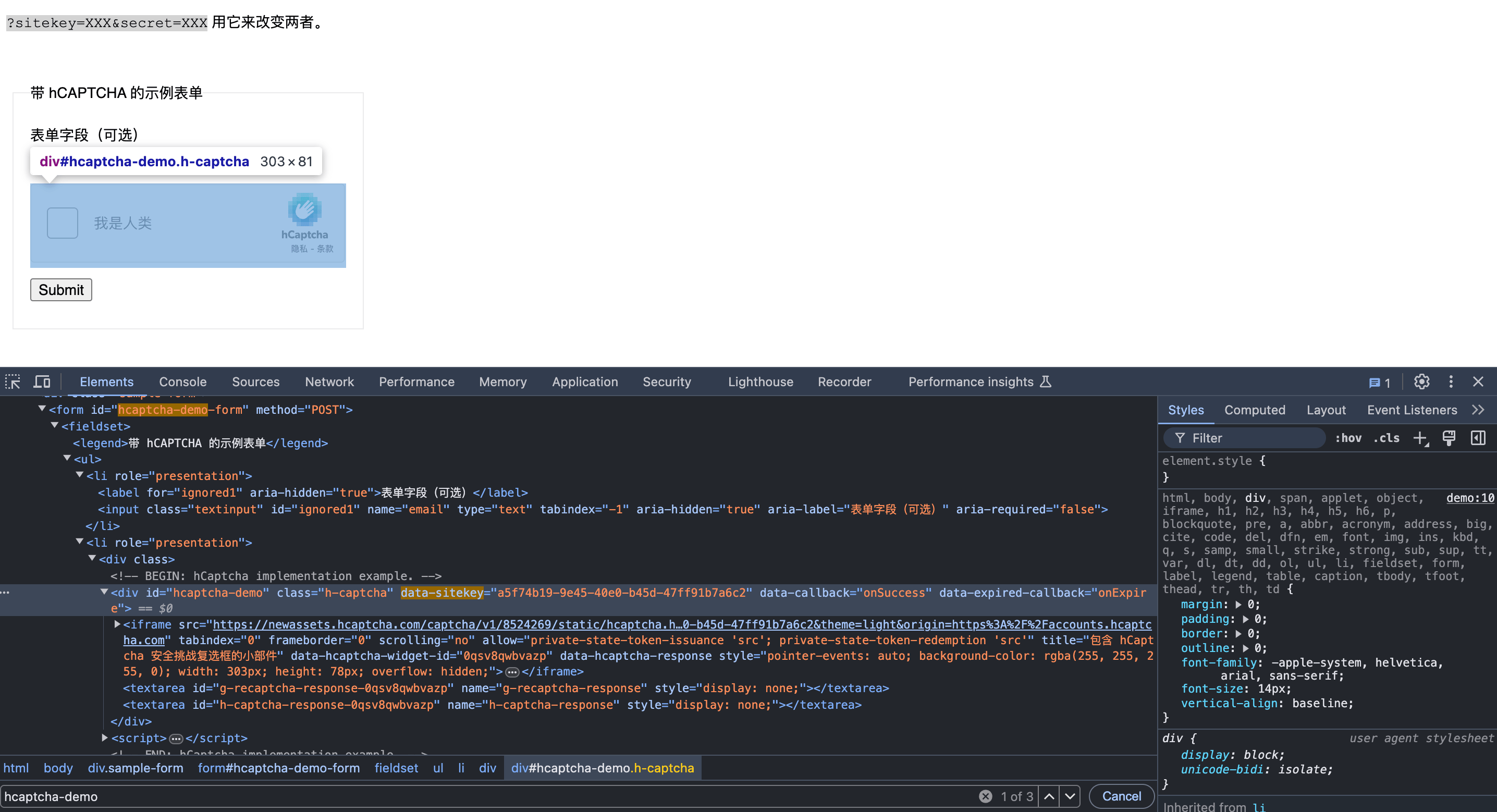
data-sitekey is the value of the website_key. Below are the specific parameter results:
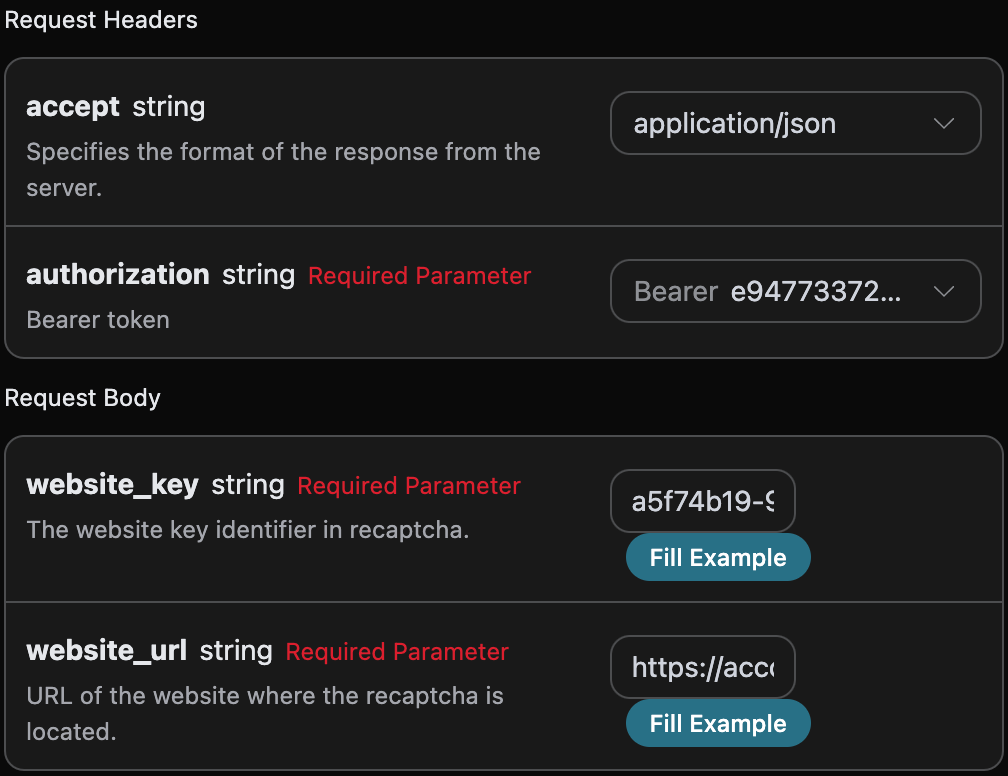
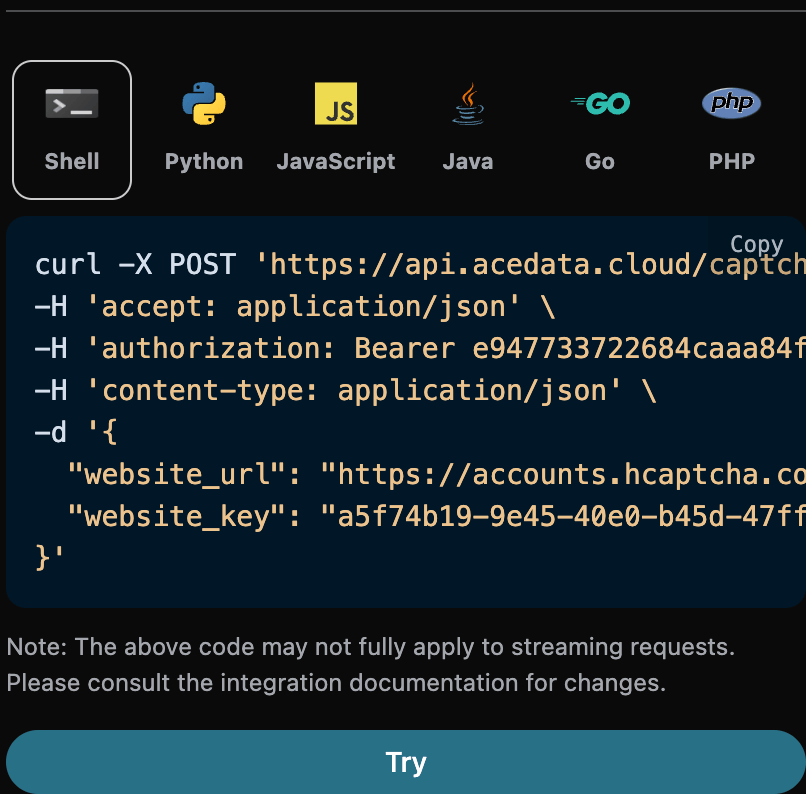
accept: the format of the response result you want to receive, filled in asapplication/json, which is in JSON format.authorization: the key for calling the API, which can be selected directly after application.
website_url: the URL of the website that needs to process the verification code.website_key: the website key identifier in hCaptcha.
- First, manually go through the verification, as shown in the figure below:
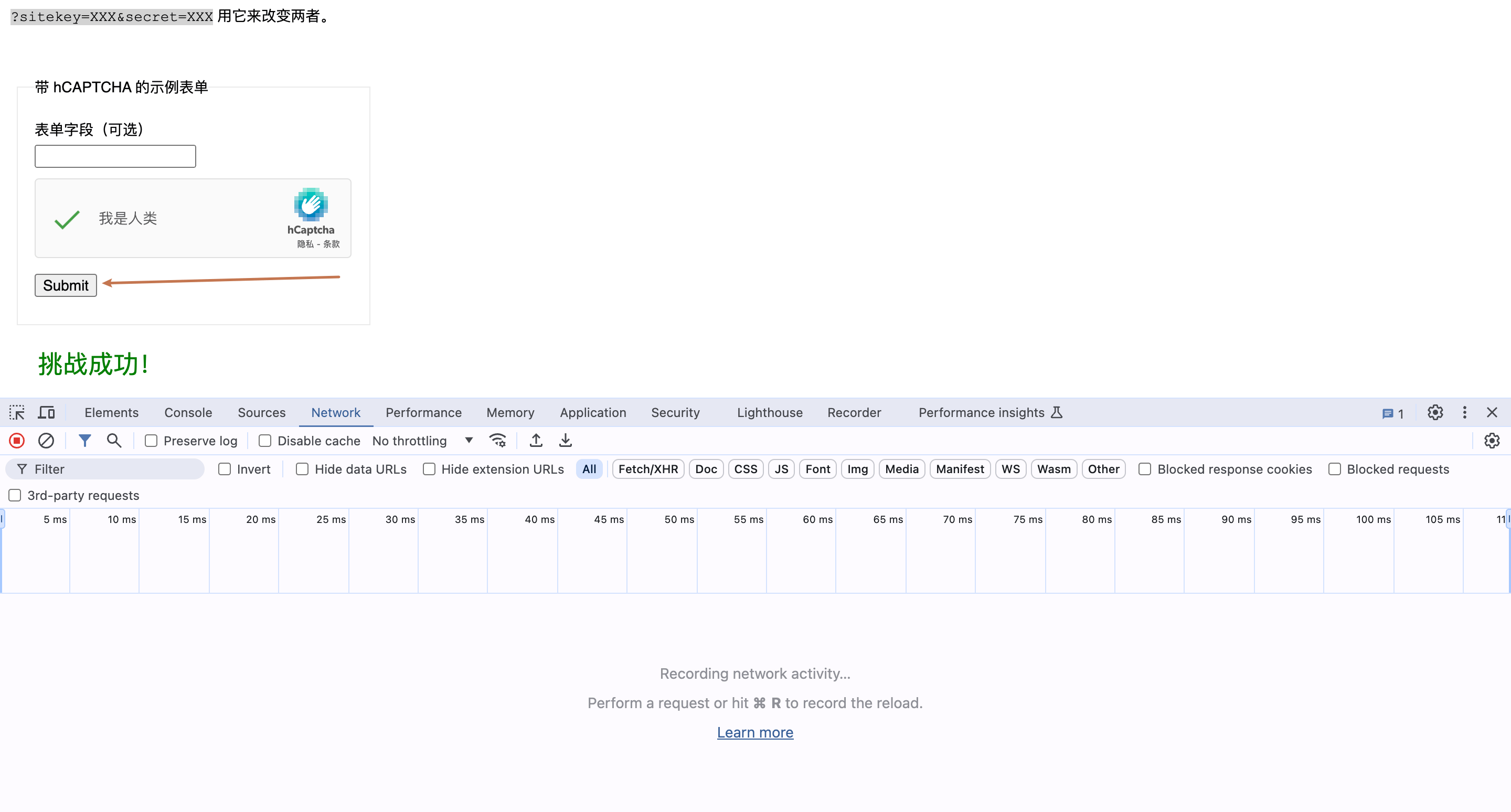
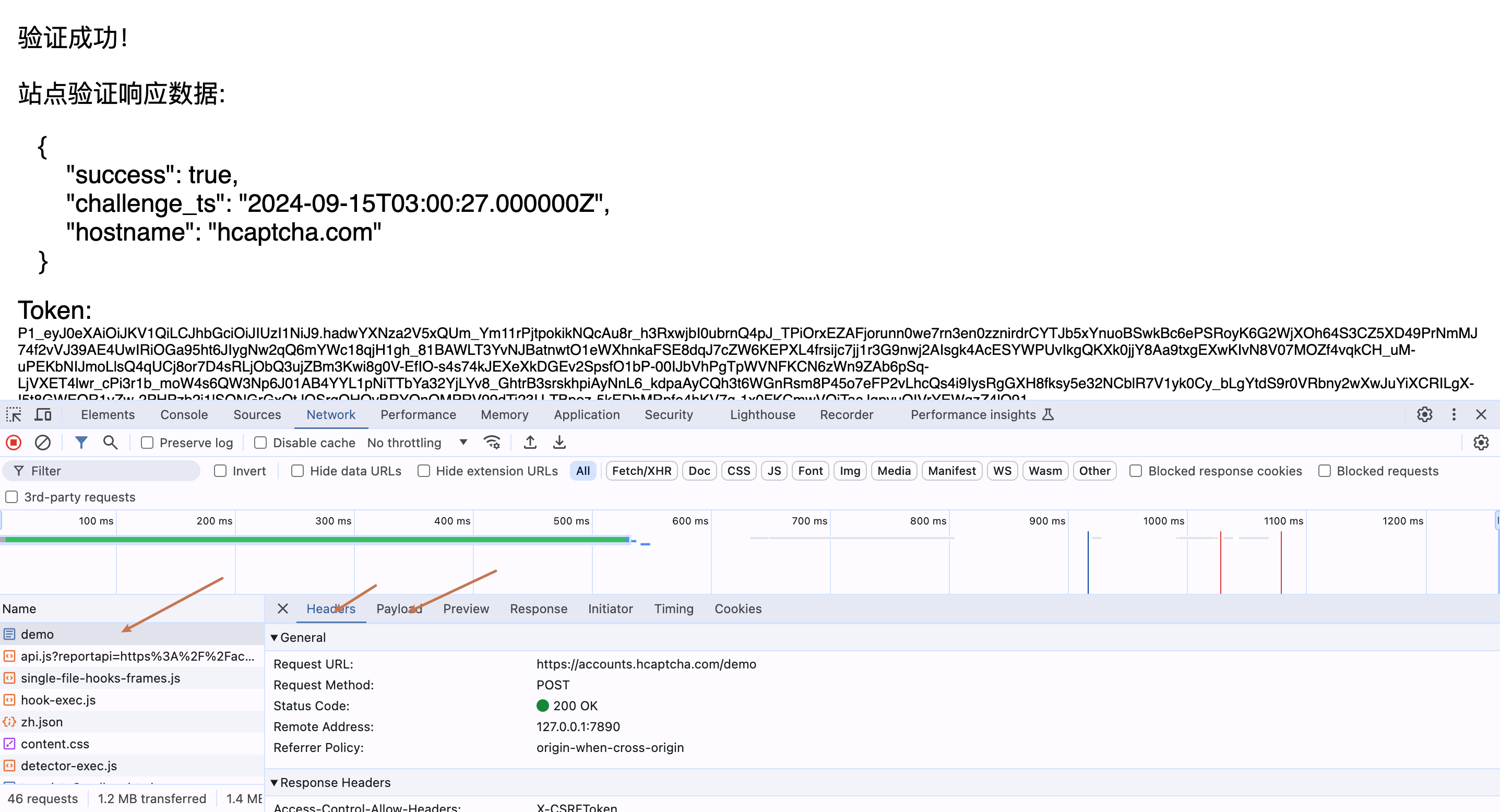
- Then click submit and watch the changes in the console’s network, as shown in the figure below:
- Analyze the construction of this submitted POST request, and finally right-click on the request to copy the CURL code, as shown in the figure below:
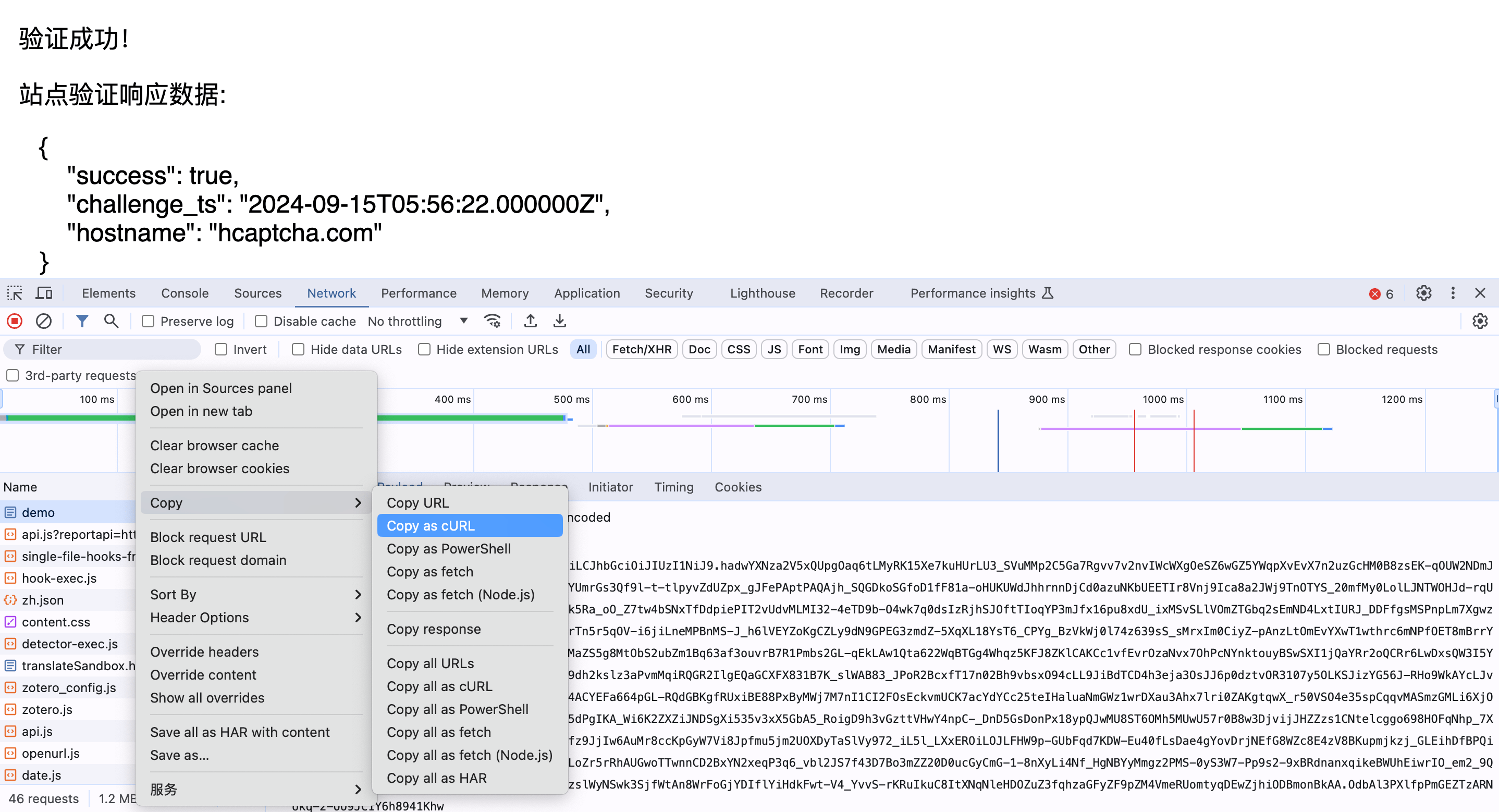
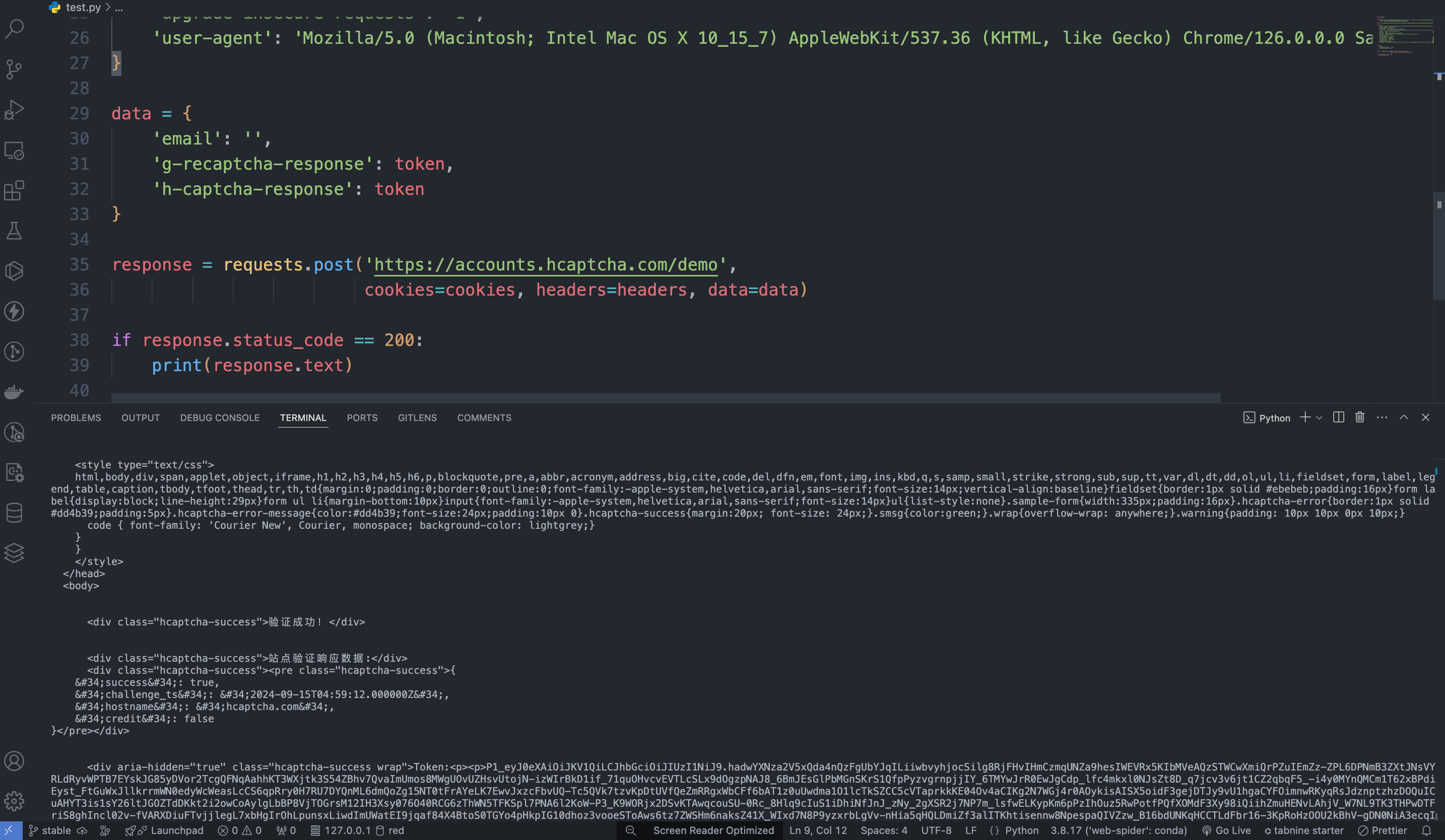
https://accounts.hcaptcha.com/demo, and we only need to submit the parameters g-recaptcha-response, h-captcha-response, and email. Then we just need to pass the processed token into the data below, and the corresponding CURL code for calling the token verification is as follows:
Error Handling
When calling the API, if an error occurs, the API will return the corresponding error code and message. For example:400 token_mismatched: Bad request, possibly due to missing or invalid parameters.400 api_not_implemented: Bad request, possibly due to missing or invalid parameters.401 invalid_token: Unauthorized, invalid or missing authorization token.429 too_many_requests: Too many requests, you have exceeded the rate limit.500 api_error: Internal server error, something went wrong on the server.

